In an
analysis by IBM
, about 26 of the 41
dating apps
studied on Android had vulnerabilities of medium and high severity.
More than 60 percent of the
most popular dating app
s on Google’s download store are potentially vulnerable to cyber attacks, which put users’ personal information at risk.
![In an [analysis by IBM]](/images/000043-1622035114.jpeg)
According to an analysis prepared by the IBM Security unit of the technology company IBM, about 26 of the 41 dating apps studied on the Android mobile platform had vulnerabilities of medium and high severity.
“Many of these dating apps have access to additional features such as camera, microphone, storage, GPS location and mobile wallet billing information, which coupled with vulnerabilities can make them targets for hackers,” , he notes.
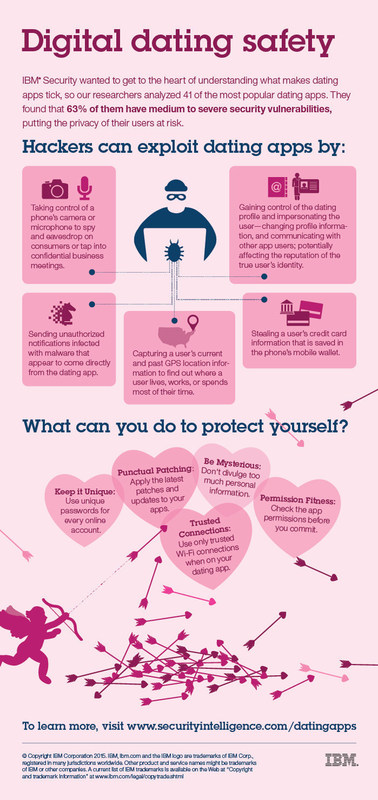
Among the main vulnerabilities discovered by IBM
is the possibility of downloading malware when the application is installed on the cell phone, as well as the use of GPS information to track users’ movements.
“IBM found that 73 percent of the 41 dating apps analyzed have access to current and past GPS location information. Hackers can capture a user’s location to find out where they live, work or hang out” .
In addition, he adds, 48 percent of the apps analyzed have access to billing information that a user stores on their device, which not only puts personal data at risk, but also users’ money.
IBM points out that by having functions that activate a phone’s camera or microphone, apps can allow a hacker to eavesdrop on users or be able to intrude on a company’s confidential meetings, even when the app is not being used.
Faced with these vulnerabilities, the technology company recommends users not to divulge too much personal information on these sites, such as where you work, your birthday or social media profiles, until you feel comfortable with the person you are interacting with.
Also, he adds, it is important to verify the accesses that will be authorized to the app, since it is common that when updated, these tools automatically reconfigure the permissions that determine which phone features they have access to, such as address book or GPS data.
“Use unique passwords for each online account you have. If you use the same password for all your accounts, you may leave multiple attack fronts open in case one account is compromised.” .